How well do you know your actual attack surface? The CANCOM Red Team shows where your organisation is really vulnerable. We carry out targeted, practical attacks on your company to identify risks at an early stage and strengthen your resilience in the long term.
Our modular approach goes far beyond traditional penetration tests: from social engineering and darknet analyses to cloud, OT and AI audits, we uncover hidden vulnerabilities and create the basis for future-proof cyber defence.
RED Teaming: Realistic attack simulations for maximum cyber resilience
RED Teaming focuses on identifying and exploiting security vulnerabilities in a company's IT infrastructure. This involves adopting the perspective of an attacker in order to simulate realistic attack scenarios and comprehensively assess the security situation. This offensive method is a central component of modern IT security strategies and complements the work of defenders such as the BLUE Teamwhich specialises in defending against such attacks.
RED teaming methods and tools
Red teaming refers to a variety of techniques, tactics and procedures (TTPs) that are used to specifically uncover vulnerabilities in the IT security process . In contrast to traditional penetration tests, which identify as many vulnerabilities as possible in a structured manner, a red team relies on realistic simulations of complex cyber attacks. The aim of red teaming is to test a company's response and resilience to potential threats and ensure that defence mechanisms are effective.
This offensive security strategy not only uncovers vulnerabilities, but also identifies structural weaknesses that could jeopardise the overall level of security in the long term. The Blue Team gains valuable insights for the defence from the activities of the Red Team, creating an effective interplay that continuously improves the organisation and ensures that identified vulnerabilities are eliminated in the long term.
Advantages of RED teaming
Red Teaming offers companies an effective way to test and improve their IT security under realistic conditions. Through the targeted simulation of realistic cyber attacks, potential vulnerabilities in IT systems, applications and business processes can be recognised at an early stage and closed in a targeted manner. A Red Team consists of experienced security experts who act like real attackers and use a variety of methods and tools to uncover specific vulnerabilities.
The use of Red Teaming not only enables the evaluation of existing security measures, but also supports the development of future-proof strategies to recognise attacks at an early stage and respond to them effectively. Once the attack phase has been completed, valuable insights and highly specialised IoC (Indicators of Compromise) are developed in close cooperation with the defenders(Blue Team) to strengthen the defence and improve the Blue Team's ability to respond.
see also: Cyber Defence Center
RED Teaming
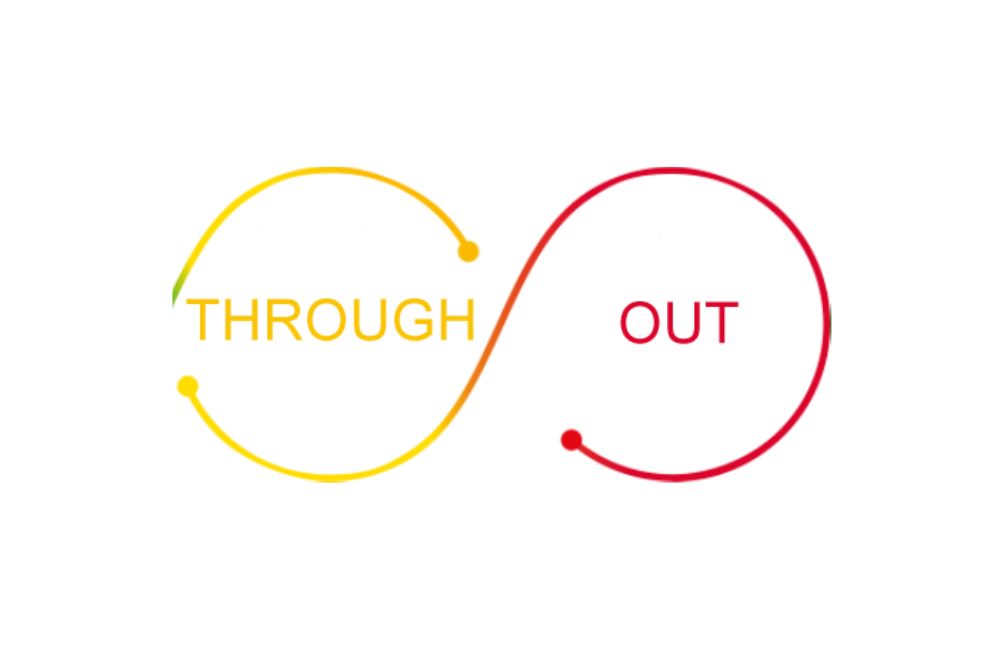
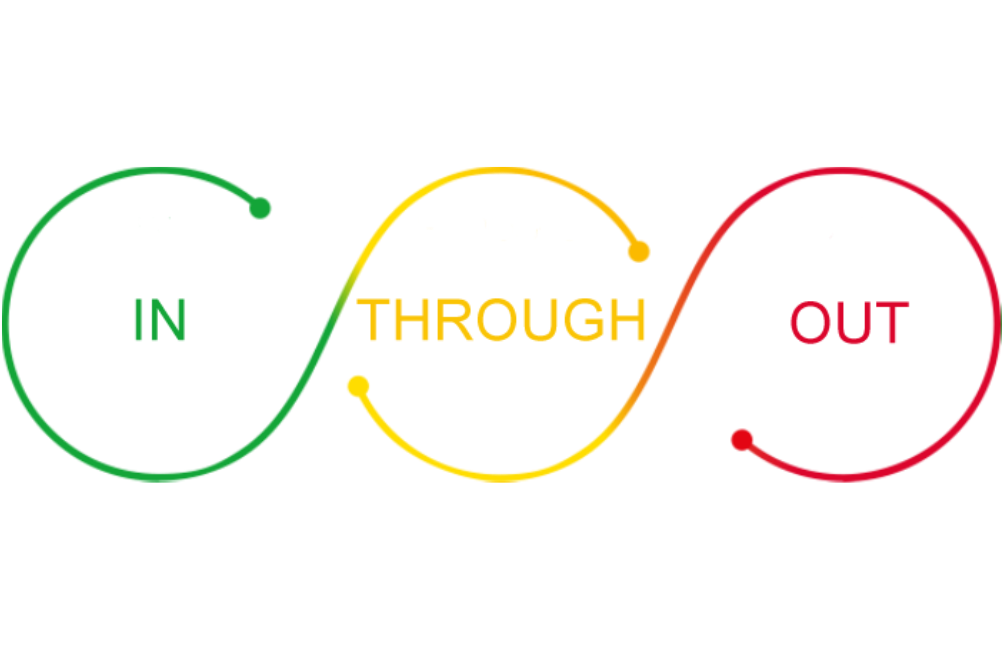
IN, THROUGH, OUT
// we transform for the better
- Based on TIBER-EU (European Framework for Threat Intelligence-Based Ethical Red-Teaming)
- Modern method of constantly and preventively increasing one's own resilience to cyber attacks and consistently putting it to the test using modern methods
RED Team - Breaching
IN
Simulation of an attacker without restrictions trying to gain access to the internal network
- Verification of the complete external perimeter (systems, personnel, ...)
- Coverage of various realistic attack scenarios
RED Team - Assumed Breach
TROUGH, OUT
Simulation of an unrestricted attacker attempting to spread through the internal network to achieve specific goals
- Checking the internal attack vector including the defense mechanisms and IT security processes
- Coverage of various realistic attack scenarios
Test -Your -SOC
TROUGH, OUT
Checking how far an attacker can penetrate the company without being detected by the Security Operations Centre (SOC)
- Tests are divided into different phases in order to recognise the reaction time of the SOC
PURPLE Teaming
TROUGH, OUT
In cooperation with the SOC team, defined targets are worked towards in order to simulate various attacks
- Indicators of Compromises (IoCs) are generated for the SOC team through the replay workshop
- The IoCs can be used to establish rules so that attacks can be detected more quickly in future
PENTest vs. Red Teaming
Pentest modules
Categorised according to the logic of the Unified Kill Chain
.png)
OSINT - Darknet Snapshot
Open Source Intelligence, one-time collection, investigation and analysis of freely available information about the company and evaluation for further attack scenarios.
- Critical information
- Searching the darknet for company-specific data
- Search for internal company documents
.png)
External pentest
Simulates an attacker from the Internet.
- Checks the IT infrastructure accessible via the Internet (e.g. mail, FTP and VPN servers, web applications)
- Without social engineering
.png)
Pentest application
Cloud/web/mobile/client check
- Security of the application logic and possibly the underlying server/OS infrastructure
- Testing in accordance with relevant standards and norms (e.g.: OWASP API Security Top 10, OWASP Top 10, OWASP Mobile Security)
- Incl. source code analysis as required
.png)
Social engineering - human pentest
Testing the IT security awareness of employees through targeted attacks on human weaknesses.
- Simulation of wide-ranging and targeted phishing campaigns
- Phishing/vishing/smishing attacks
- Pre-texting and water-holing
- ...
.png)
Social engineering - site pentest
Verification of physical security and reaction to unauthorised access.
- Intrusion simulation and site inspection by means of night operations (implants, C&C setup, simulation of disposable agents, ...)
- Inspection of the site (clean-desk policy, ...)
- Active influencing of employees (pretexting, impersonation, tailgating, ...)
- Dumpster diving, USB drop
.png)
Internal pentest
Simulates an attacker who could gain access to the internal network.
- Checking the internal network (Active Directory, file shares, applications, ...)
.png)
OT Pentest
Review of network compartmentalisation, company-wide with a focus on access to the production environment
- Evaluation of the security of the production environment based on relevant standards and norms
- Testing of SCADA and control technology networks (OT)
- Review of access control/remote maintenance
.png)
AI Pentest
Verification of AI and its secure integration into the IT structure
- OWASP Top 10 principles for machine learning
- Data leakage
- Prompt injection/jailbreaks
- Supply chain vulnerabilities/sensitive data disclosure
- Data poisoning/overreliance
- Model theft
.png)
Special pentest
Verification of specific security requirements that go beyond standardised tests
- Customised solutions for unique business processes and IT systems
- Integration of new technologies into existing security concepts
- Analysis and evaluation of highly specialised IT infrastructures
- Flexible customisation to individual security requirements
Regulatory compliance
Red Team Security Reports
Transparent security reports for management and technical teams
We understand that reports are an essential part of our service provision. Our reports are therefore essentially divided into two areas:
- Executive summary for management
- Detailed findings for the technical team.
Of course, we not only provide you with the findings themselves, but also an assessment of the weakness and a recommendation on how you can rectify it.
Qualified inspection body within the meaning of the NISG
Fulfillment of necessary requirements, which are also validated accordingly by the BMI
- Experienced auditors
- Security-cleared auditors within the meaning of the Security Police Act (§ 55a para. 2 SPG)
- Taking own security precautions (e.g. ISO27001 certification)
- Use of suitable hacker tools
- Application of a suitable testing process
- Appointment by decision
- Companies with a head office and registered office in Austria
Tried and tested







.png)
.png)
Our IT security services
Contact
CANCOM Austria
Enquire now

-1920x1013.jpg)